End-to-end encryption, by default
Every message, every attachment, every group invite. The server sees ciphertext and routing metadata — never your content, never your contacts list, never the channel name.
XCHACHA20-POLY1305 · X3DH + DOUBLE RATCHET
End-to-end encrypted · No accounts · Open protocol
Hutor is a messenger where your identity lives in twenty-four words you keep yourself. No email, no password, no central account — just keys, on your devices, under your control.
What it is
Four properties define Hutor. Each one is a constraint on how the product is built — not a marketing checkmark.
Every message, every attachment, every group invite. The server sees ciphertext and routing metadata — never your content, never your contacts list, never the channel name.
XCHACHA20-POLY1305 · X3DH + DOUBLE RATCHET
Your identity is a deterministic key derived from a BIP-39 mnemonic. There is no email field. No password reset link. Whoever holds the words holds the account — and that is the point.
BIP-39 · ED25519 · DETERMINISTIC
Add a phone, a laptop, a tablet. Each device is a peer. A priority chain decides who decrypts incoming messages first; if the primary is offline, the next picks up — without round-trips through a server.
PRIORITY FALLBACK · PER-DEVICE KEYS
Per-channel aurora tints. Light or dark. Compact or generous. Reactive bars or a flat gradient. The chrome adapts to you — not the other way around — because a messenger you stare at all day should not be hostile to look at.
AURORA · BARS · PLAIN · CUSTOM GRADIENT
How it works
From "I want to try this" to "I just sent my first encrypted message" in under a minute.
Hutor draws a BIP-39 mnemonic in your browser. Those words are your private key — the only thing that proves the account is yours. Write them down somewhere you trust.
CLIENT-SIDE · NEVER LEAVES YOUR DEVICE
Cosmetic, not authentication. The username is a public handle so people can find you; the account is still cryptographically anchored to your words. If somebody else takes the username, your keys still work.
PUBLIC HANDLE · IDENTITY UNCHANGED
Search for someone, send an invite, open a channel. Every message from this point on is end-to-end encrypted. Your devices keep a local copy; the server only sees ciphertext.
E2E · MULTI-DEVICE · OFFLINE-CAPABLE
A look at it
The aesthetic is not decoration — it is part of how the product behaves. Channel-tinted backgrounds, glass surfaces, per-message hover affordances. Scroll the screenshot.
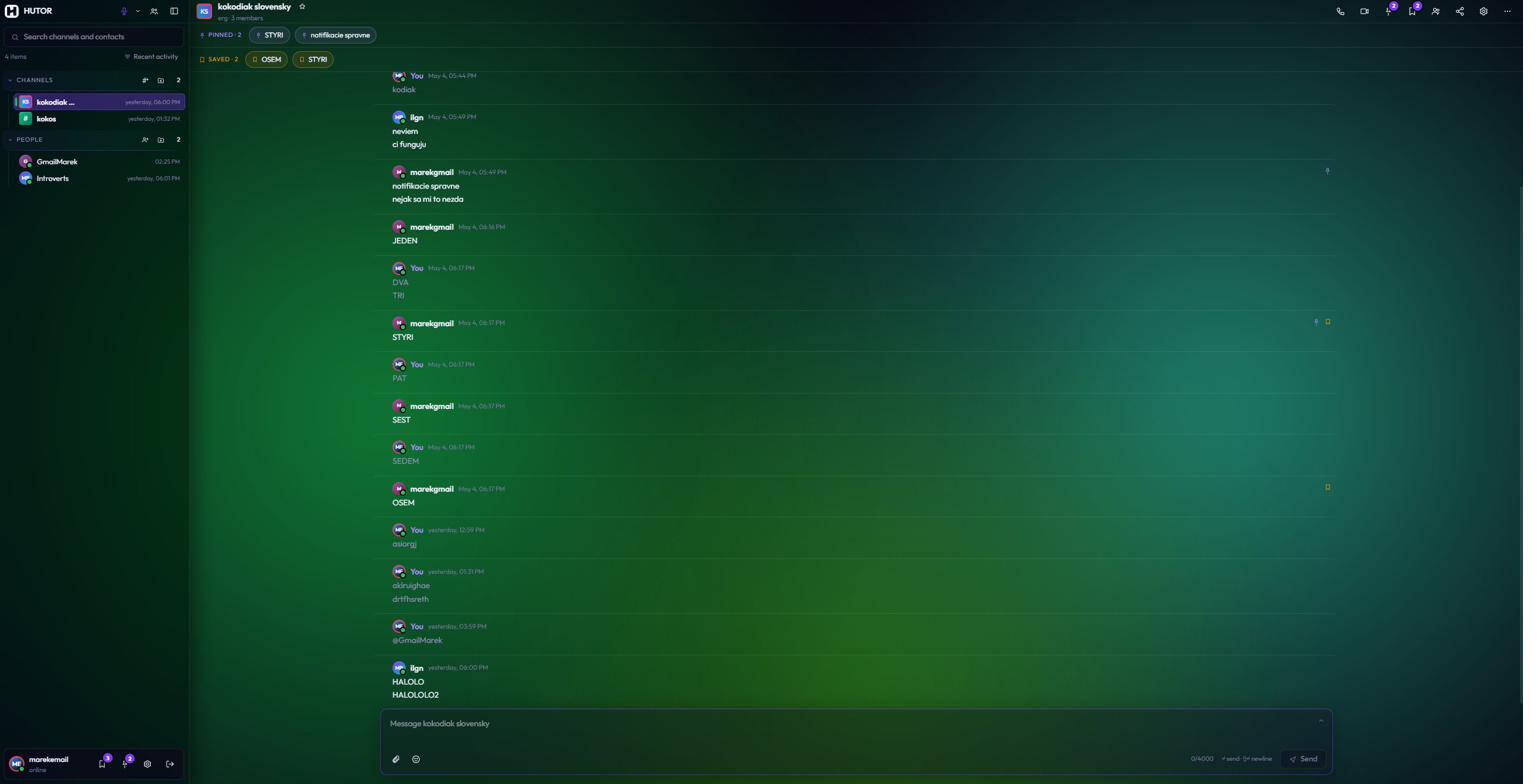
Group channels and 1:1 conversations live in the same sidebar. Every entry is a cryptographic peer — there is no organisational layer above your contact list.
Each channel and contact has its own colour palette derived from its identity. The background tints to match — so glancing at the window tells you where you are without reading.
Timestamps, status rows, technical labels — all in JetBrains Mono with a soft tracking. The chat itself stays in proportional sans, so the typography hierarchy reads at a glance.
Why mnemonic
Most messengers anchor your identity to a phone number or an email address. That is convenient, and it is also the part of the system that is least under your control. A SIM swap, a hijacked email, a vendor closing your account because of an automated content scan — any one of these severs you from your conversations permanently. The keys were never really yours.
Hutor takes a different position. Your account is a deterministic cryptographic key derived from a twenty-four-word seed. The seed is generated on your device, never transmitted, never stored in a database we can be compelled to hand over. There is no password because there is nothing to reset; there is no email because there is nothing to recover.
The only person who can lock you out of your account is yourself.
This trade is honest about its costs. If you lose all twenty-four words and all your devices at once, the account is gone — and nobody, including us, can bring it back. We think that is a feature, not a bug. The alternative is a recovery channel, which is just another word for backdoor; once it exists, somebody other than you can walk through it.
In exchange you get something that is rare in modern software: a relationship with a service in which the operator is structurally unable to read your messages, suspend your account at the request of a third party, or hand over a list of your contacts. Not because we promised. Because the protocol does not let us.
FAQ
If you have another device that is still signed in, write down a fresh export of the same mnemonic from there immediately. If you have lost every device and the words, the account is unrecoverable — that is the deliberate consequence of having no backdoor. We strongly recommend writing the words on paper and storing the paper somewhere physical and durable.
No. Messages are encrypted on your device with keys derived from your mnemonic before they ever leave it. The server stores ciphertext and routing metadata; it has no access to plaintext, channel names, or your contact graph. The same is true for attachments.
You can keep reading and composing locally. When the server returns, queued messages flush. The protocol is being designed to support self-hosted relays, so you do not need to trust us as the only operator — you can run your own and federate.
Each device generates its own key pair from the same mnemonic. A priority chain — set in Settings → Devices — decides which device decrypts an incoming message first. If the primary is offline for more than the configured threshold, the next device in the chain takes over.
Hutor uses well-studied primitives (XChaCha20-Poly1305 for symmetric encryption, X3DH and Double Ratchet for forward-secret messaging, Ed25519 for signatures). The protocol layer is open source and has been reviewed by external cryptographers; the audit reports are linked in the security page.
Because the moment we collect one, we become a single point of compromise — a target for SIM swaps, account takeovers, subpoena pressure, and automated content moderation that locks people out of their conversations. Removing the field is the only way to make those attacks structurally impossible.
Yes. Channels support multi-user threads, link previews, file attachments, message editing and deletion, pinned messages, and per-channel notification preferences. A team-oriented mode with shared admin tooling is on the roadmap for organisations that want to self-host a relay.
The protocol and client are open source under a permissive license. The server reference implementation is open source under AGPL — anyone can run a relay; anyone can audit how messages are routed. Links are in the footer.